If you’ve stumbled on or were directed to this page, you may be one of the many people asking “How do I get a job working in Cyber or Information Security” or rather where do I find resources. I get this question often and not always from people locally so I put a few notes together. The answer to this question has also evolved as this is my regarding this topic. Check out part 1 and part 2, then come back here.
Continue readingPage 2 of 13
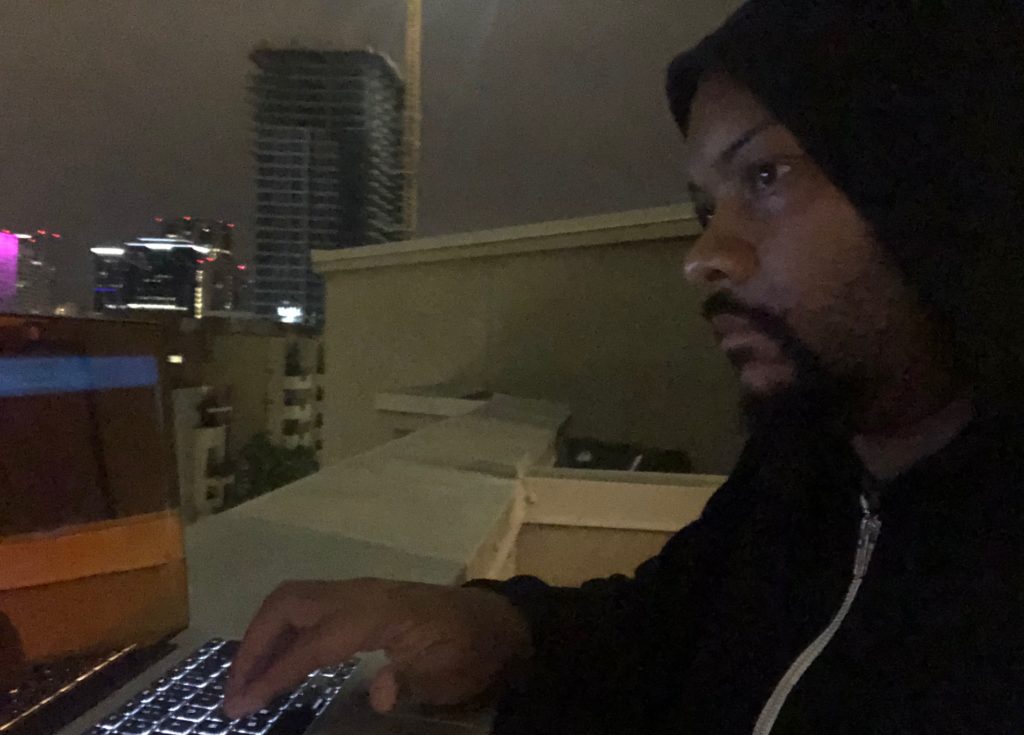
The BirdFeeder
As I’ve been cutting my teeth in the PWK labs I’ve been working on doing things more efficiently, specifically to save time. I remember reading a chapter of POC|GTFO that specifically mentioned “building your own birdfeeder” that I particularly liked regarding building your own toolset. Some people ask, “why not just find your own tools”?
Continue reading