In my first Infosec role, a part of my job was to manage quarantine queues, adding mail domains to any white or black lists based on their reputation. While I could just go to sites like Virustotal or Senderbase and manually enter the URLs in, that would just take the fun out of it. The idea of the tool came from me wanting to sharpen my Python skills, and get some experience scraping useful public information on the Internet. I’ve written pretty simple scripts in the past and wanted to learn more than just the basic provide input–>get output.
CategoryBlue
Reverse Engineering: From newb to 0x001337AF
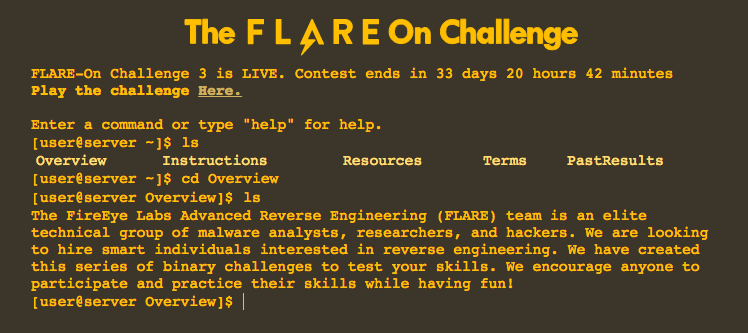
Back in September, FireEye began their third annual FLARE-ON reverse engineering challenge. This is basically a reverse engineering themed CTF that lasted about six weeks. This was my first time getting some hands on experience with Reverse Engineering so while I learned a lot, there is still much more to go. Keeping in mind this is my first time really diving into reverse engineering, i’ll start off with what I knew at the start:
My dad: “So is it kind of like taking a car apart down to its individual pieces”
Me: “No, not kind of. It is exactly like that! That’s how people find out how malware works and how programs can break”
This was an earlier conversation with my dad about RE and a summary of what I knew before deciding to take on this challenge. In between work and everything else, I didn’t make it too far this time around only finishing the first challenge (with some help). If nothing else I took away from this CTF, like many others learning the tools and which tools are the most effective is just as important as learning the craft.